
How to be proactive with Google Cloud Security Command Center Findings
Google Cloud’s Security Command Center (SCC) provides a unified view of all potential security issues in your cloud environment. But what happens if you don’t have time to review the findings discovered, or simply forget? If you don’t check, that open firewall will remain open, or that storage bucket will remain public without its content having been reviewed.
What if you could be more proactive with these findings and get notified in real-time?
In this post, we’ll go over how to extend the power of SCC Findings by adding the ability to set up alerts with Cloud Monitoring.
How it works
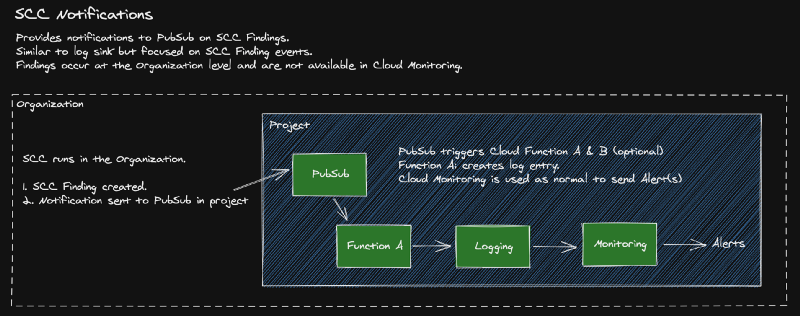
A shortcoming of SCC is the lack of metrics and alerting via Cloud Monitoring since Findings are only visible at the Organization Level. By exporting findings into PubSub [1], along with this project’s scripts, you can make notifications available in Cloud Monitoring.
With this project’s scripts, you will:
- Automate the setup and removal of SCC Notifications to PubSub into your project
- Log the Findings into your project, making the data available to Cloud Logging & Cloud Monitoring
- Remove or reduce any custom scripts to be created and use standard GCP features where available
Requirements
To run the scripts you will need the following.
- Organization ID — where your project is located
- Project ID — where the resources will be installed
- Service Account — a service account for SCC Notifications to run
- The following APIs must be enabled for the project: Security Command Center API for the Organization, Cloud Build API, Cloud Functions API
- You will need IAM security roles of
- Security Center Admin — to set up notifications
- Organization Admin — to set up the service account with needed roles
Installation
Clone the repository
Clone the repo to Cloud Shell. Optionally, clone to a VM or your local machine if you prefer.
git clone
https://github.com/gschaeffer/scc-findings-to-pubsub
Edit variables
Edit the script variables in the setup.sh file. You must edit the organization id, project id, and service account values. The remaining variables are optional.
Run setup
First, we install the SCC Notifications to PubSub as described by Google [1 above]. Use the setup.sh command which automates this process. Be sure that your gcloud config is set to your project ID.
gcloud config set core/project YOUR_PROJECT_ID
./setup.sh apply
# if prompted with 'API [securitycenter.googleapis.com] not enabled # on project. Would you like to enable and retry?', select 'y'.
This creates only the resources as described in the SCC Notifications doc [1]. At this point, you should begin seeing notifications being sent to the PubSub topic as they are identified in SCC.
Add a Cloud Function
Second, to make Findings events available in Cloud Monitoring, install the provided Cloud Function. This will begin sending Findings from PubSub to Cloud Logging & Cloud Monitoring. The install script is in the functions directory.
cd functions/ ./deploy_logger_func.sh
This installs a very simple Python function that will be triggered by Findings being added to the PubSub Topic. After installing, you should begin seeing log entries in Cloud Logging. These entries are logged into a log named scc_notifications_log for easy search.
With the Findings in Cloud Logging, all the normal Google Cloud tools & services are available to setup Metrics and Alerts https://cloud.google.com/monitoring/alerts. If you’d like to work with this data in BigQuery, Cloud Storage, or even another PubSub Topic then you can use Logging Exports https://cloud.google.com/logging/docs/export to push the data to your preference.
Cleanup
To remove the resources installed use the same setup command with delete argument and gcloud to remove the cloud function. Change the function name and region variables as needed.
./setup.sh delete FUNCTION="scc_notification_handler" REGION= gcloud functions delete $FUNCTION --region $REGION
Originally published at https://github.com.


